Let's get cracking
The fascinating story of how software piracy became an art form
Let’s say, just for argument’s sake, that you happen upon a hacked version of a PC game and run installer.exe. To the plonky sounds of synth music you might read, “Tony Hawk Pro Skater 4 (c) Aspyr. Enjoy another nice game from your friends at Class.” After that, you open the accompanying .nfo text file. Beneath an ASCII art graphic, you read details about how the game was ripped, and a ‘help wanted’ section, seeking partners in crime like suppliers, distributors, and the elite of videogame lawbreakers: crackers.
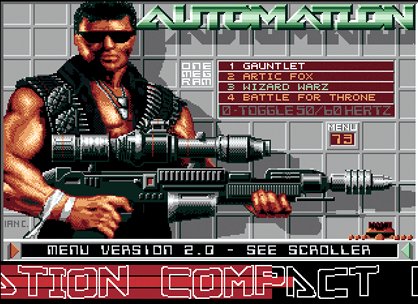
Back in the day, cracker groups were borderline famous. With names like Criminal Disguise, X-Static, G-Force, Now5 and Automation, they sounded like south London grime crews - but instead of laying down ‘wicked rhymes’, these posses gouged out the guts of PC games, wedged a few personal mementos inside, then sewed them back up again. Some pirates have little more than mischief in mind you see, in stark contrast to their public image of morally repugnant individuals who somehow manage to fund terrorism.
“There is a strong social aspect to the cracking scene,” says Ben Garrett, who runs Defacto2.net, a site dedicated to the computer underground counterculture. “It’s part of the reason why people contribute so much time, effort, even money into their various roles and why they often find it hard to detach from it. Today’s scene is nowhere near as social as it was in the ’90s and ’80s. Back then, consumer piracy was a civil, not a criminal issue and the risks and paranoia just weren’t there.”
In fact, home piracy began in 1975 with the first commercial program for a microcomputer: Microsoft’s Altair BASIC. “Most users of this now legendary system were hobbyists who actively encouraged the copying and sharing of programming code,” says Garrett. Mass piracy wasn’t exactly a burning issue, though, since cassette games deteriorated after each copy. In 1978, Apple’s Disk II floppy disk drive changed all that, and software publishers, seeing a fleet of marauding brigands on the horizon, hurriedly introduced copy protection.
Weekly digests, tales from the communities you love, and more


